Find exposed internet-facing assets before you're attacked
Get Expert Guidance to Fix Them Fast
AI can now write highly effective exploit code in minutes, and criminals can start attacking within the hour. Halo’s fast, affordable external attack surface management platform helps you find these exposed assets and vulnerabilities first.
Halo Security continuously discovers, monitors, and prioritizes risk across your external attack surface—including unknown assets, forgotten cloud services, and third-party exposures most tools miss. And unlike traditional EASM tools, Halo includes expert remediation guidance at no extra cost, so your team can act with confidence.

Halo is Trusted by Security Leaders
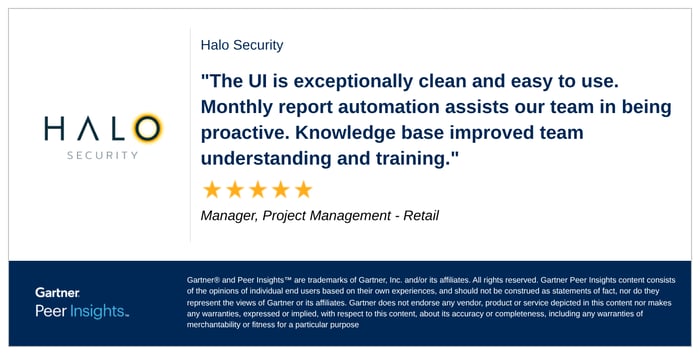
What do real customers say? Halo Security scores 4.6/ 5 stars with 95 independent customer reviews on Gartner Peer Insights.
Halo provides:
-
Daily, automated asset discovery with no agents to deploy
-
Visibility into forgotten projects, shadow IT, and cloud sprawl
-
Optional connectors for AWS, GCP, Azure, and Cloudflare
And when questions arise, our experts are available to help you interpret findings and decide what to tackle first.
Get context you can act on
Raw asset lists don’t reduce risk—understanding does. Halo enriches every asset with the context you need to know what it is, what’s running on it, and why it matters.
-
Search and filter assets by technology, ports, geography, and risk
-
Automatically tag and organize assets using advanced rule sets
-
Group targets by environment, business unit, or subsidiary

External risk management built for today’s reality
Today’s attack surface is dynamic, distributed, and constantly changing—spanning cloud environments, SaaS platforms, subsidiaries, and third-party providers. With attackers using AI to write exploits in minutes, your external attack surface is more vulnerable than ever.
Halo Security takes the attacker’s perspective to show you what’s truly exposed on the internet, then pairs that visibility with practical expert guidance to help today’s resource-strapped teams reduce risk quickly. Learn how our platform delivers continuous scanning and expert guidance to deliver fast, affordable risk remediation during a no-pressure demo that shows you a complete picture of your external attack surface!
Not quite ready to schedule a demo or trial? Keep reading for more information.
Take an Interactive Tour of our Platform
Four Advantages of Halo
Uncover real-world risks beyond CVEs and eliminate them faster. Attackers don’t limit themselves to known vulnerabilities, and neither should your security program. Halo Security detects CVEs and the exposure issues scanners routinely miss. But not all findings deserve equal attention. Halo helps you focus on the risks most likely to be exploited—and helps you fix them efficiently.
Prioritize with confidence. We prioritize the alerts and curate the context so you can efficiently remediate issues without sifting through a time-consuming data dump. You can:
- Track risk scores across assets, asset groups, and your full attack surface
- Prioritize issues using severity ratings and the Known Exploited Vulnerabilities (KEV) catalog
- See clear remediation guidance for every issue
- Assign and track remediation progress across teams
Expert help when it counts. For high-impact or complex findings, Halo’s security experts are available to help you validate severity, understand exposure, and provide guidance on the most effective remediation path.
We’re built for the way mid-market teams actually work at a price they can ac. Most EASM platforms assume large teams, dedicated analysts, and unlimited time. Mid-market organizations operate differently. Halo Security delivers enterprise-grade external visibility with expert remediation guidance included and designed to help lean security teams reduce risk quickly.
A FEW OF OUR CUSTOMERS





